Access governance software is a system used by organizations to manage user access to information technology (IT) assets, such as applications, databases, and network resources. The purpose of this software is to ensure that only authorized users have access to IT resources and that their access privileges are appropriate and in compliance with corporate policies, government regulations, and industry standards.
Access governance software is built on a set of powerful features that enable organizations to optimize their security posture. These features include identity and access management (IAM), role management, access certification, and audit and compliance reporting.
IAM is the foundation of access governance software. It involves creating and managing digital identities for users, assigning access rights and permissions, and verifying the identity of users accessing the system. With IAM, organizations can centralize user management, ensure consistent policies across the entire IT infrastructure, and reduce the risk of data breaches.
Role management is the next critical feature of access governance software. It involves defining the roles and responsibilities of users with access to IT resources. With role-based access control (RBAC), organizations can provide users with the minimum privileges required to perform their job duties and monitor their activity, allowing them to rapidly detect anomalies and reduce the risk of insider threats.
Access certification is a process that ensures that all user access privileges are aligned with corporate policies regularly. By enforcing regular certification campaigns, organizations can quickly identify issues with access permissions so they can be resolved before they cause security breaches.
The final feature of access governance software is audit and compliance reporting. It involves tracking all user access events, analyzing them, and producing reports to ensure adherence to corporate policies and regulatory requirements. With audit and compliance reporting, organizations can maintain visibility into user activity across the infrastructure, detect compliance violations, and take corrective actions.
The benefits of access governance software are significant. In addition to improving the security posture of organizations, access governance software can also increase operational efficiency, enhance user productivity, and reduce the cost of compliance.
One of the primary benefits of access governance software is that it allows organizations to automate and centralize their user management processes. This helps IT teams streamline many tasks related to user access. For example, with a single source of truth for user data, IT teams can efficiently provision and de-provision access for users as they enter or leave the organization.
Access governance software also enables organizations to reduce the risk of data breaches and limit damage from insider threats by implementing RBAC policies. With RBAC, organizations can provide the minimum necessary access for each user based on their job duties, meaning that an insider with malicious intent would have limited or no access privileges to sensitive information or systems.
Another significant advantage of access governance software is enhanced user productivity. With a clear understanding of user roles, IT teams can ensure that users have access to the resources they need to fulfill their job responsibilities and that they have the necessary permissions to use them. This eliminates the need for users to seek help in getting access, saving them time and frustration and enabling them to focus primarily on their work tasks.
Finally, access governance software can help organizations reduce the cost of compliance. By providing clear audit trails and reports, organizations can rapidly demonstrate compliance and avoid costly fines by regulators.
Access governance software is a fundamental solution for organizations that want to improve their security posture, achieve operational efficiencies, enhance user productivity, and reduce the cost of compliance. By implementing access governance software, organizations can centralize user management, eliminate the risks of human error, and ensure that users have appropriate access privileges. With access governance software, organizations can safeguard their IT infrastructure and protect their data, applications, and network resources from cyber threats.
NETWRIX

Reduce the chance of data breaches by making access to sensitive data exclusive with data access governance software from Netwrix.
- Focus your data security efforts on the most critical data
- Monitor security risks and report your progress
- Identify the most significant risks around your data and close those gaps first
- Prove the security of personal information and respond promptly to DSARs
AVATIER
Avatier access governance software compliance auditor features access certification and group enforcer automates group management software for governance risk and compliance management.
- Reduce Costs
- Increase Productivity
- Achieve Compliance
- Increase Security
- Wizard-Enabled
- Prevent Mistakes
ONEIDENTITY
One Identity provides data access governance tools to help control access and govern data through automated requests.
- Protect and identify high-risk areas
- Empower data owners to control access
- Power to approve unstructured data-access requests
- Detect and remediate policy violations
- Automate request-and-approval workflow
- Analyze unstructured data access requests to files, folders, NAS and SharePoint
SAP
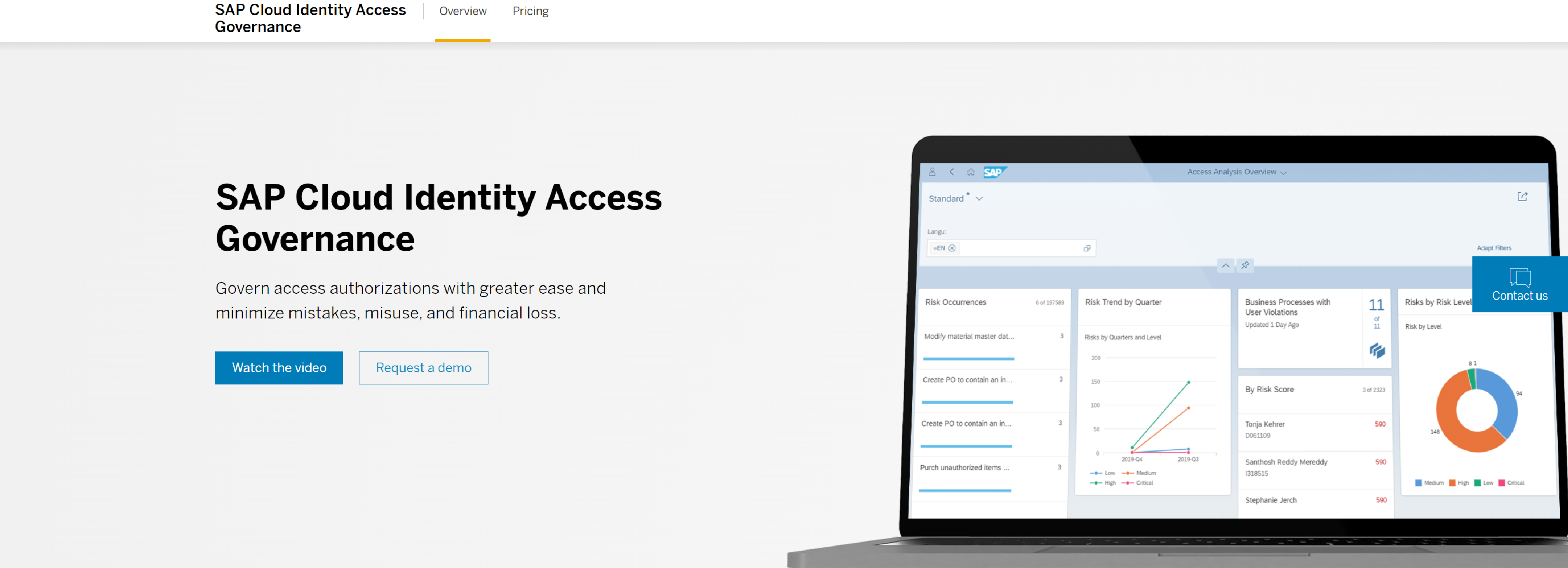
Streamline identity and access management (IAM) in complex on-premise and cloud environments with SAP Cloud Identity Access Governance software.
Features:
- Access compliance management
- Intelligent optimization of assignments
- Extended control and risk management
Benefits:
- Simplify the governance of data access
- Deliver a seamless user experience
- Adapt identity and access governance
LEPIDE
Lepide’s Data Access Governance Solution enables you to know where your sensitive data is, who and how users are accessing it.
- Classify Sensitive Data
- Stop Unauthorized Access
- Monitor User Behavior
- Detect Anomalies
- Detailed Pre-Set Reports
- Real Time Alerting
ITCONCEPTS

ITConcepts is one of the leading IT service providers for the efficient automation of IT business processes. ITSM, ITOps, IAM & Big Data.
- Reduced risk of unauthorised access to sensitive data
- Improved audit performance
- Lower operating costs
- Increased productivity for IT staff
LUMOS
Govern your apps with one platform with Lumos SaaS management and identity governance software.
- Automate Your Helpdesk
- Increase Your Security Posture
- Simplify Compliance
- Spend Less On SaaS
STEALTHBITS
Stealthbits protects unstructured data & sensitive information with data governance tools and data access governance software.
- Unstructured & Structured Data Support
- Active Directory Management & Security
- Desktop & Server Security
SAVIYNT
Embrace Zero Trust, secure sensitive & privileged access, and stay in continuous compliance with the world’s #1 cloud identity governance platform.
- Protect Critical Assets
- The Right Access, at the Right Time
- Make Smarter Security Decisions
- Solve Big Identity Challenges
- Reduce Risk & Compliance Costs
OVALEDGE
OvalEdge enables its customers to take a full-circle approach to overcome common data access roadblocks.
- Enforcement of data access policies just got easier
- The only integrated & non-intrusive data access platform
- Enforce your data access policies with a few simple steps
- OvalEdge Recognized by Industry’s Top Analysts & Thought Leaders
TORSIONIS

Simple, intelligent and effortless Data Access Governance for Microsoft 365. As users constantly share data, Torsion delivers powerfully.
- The Automated Solution
- Simple, intelligent and effortless Data Access Governance for Microsoft 365
- As users constantly share access, ‘who has access to what’ quickly gets out of control
SECURENDS
SecurEnds cloud software enables the world’s most forward-thinking companies to automate user access reviews, access certification and recertification, and entitlement audits.
- Establish a clean set of user entitlement data to support risk and compliance efforts
- Increase compliance efficiency by streamlining certification
- Automate data and controls ingestion and approval workflows
- Interactive, identity-centric view across IT risks, applications, and entitlements
- Out-of-the-box application support and IT controls
- SaaS-based platform for rapid delivery for quick time-to-value