Authentication is a process of identifying an individual or user on the basis of username and passwords, security tokens, biometrics which he or she claim to be but does not give any information about the access rights of the particular user. In the security systems authentication is well-defined from authorization, as it is the process in which the user is given complete access to the system objects based on their identity. The process is based on measure of the risk. Stronger Authentication is something the where high risk systems, applications and information needs different kinds of Authentication which accurately confirms the digital identity of the user who they claim to be, than the low risk application, where the confirmation of the digital identity of the individual is not that important when considering the risk factor.
Authentication process is mainly dependent on the identity verification and registration processes. For instance we take the example when Rachel Wiz has been hired by an employer and then she has to provide the personal information such as name, address, birth certificate, driving licence, SSN No, Passport details etc. Now it is up to the employer to accept it immediately or choose for a background check on the information provided by Rachel Wiz which she claims to be, they can also clarify whether she is having any criminal record. Once the check is completed and the results come in favour of the employer then they will confirm the identity as true and enter her details in their system. The identity process involves issuing Rachel with the employer authentication mechanisms which include passwords, digital certificates, id, security tokens and registering her biometrics.
Authentication process is purely dependent on the identity validation and the registration process used by Rachel Wiz. Think that Rachel has provided false information while the registration and which has been accepted by the employer, then the individual or user who is acting as Rachel will be always authenticated in the right perspective every single time. From this we understand that authentication is solely dependent on the information provided by the user which can be true or false, this shows the weaker side of the application.
Single Sign On Authentication
Single Sign-On (SSO) is an application where the user’s single action can authenticate, authorize and allow the user to access all the computers and systems where the user has the permission to access, without entering multiple passwords for every single login. Single Sign-On Software can regulate the components of system failures and reduce the number errors caused my humans, which is why the software is highly recommended globally. The Software is tested in different platforms of the industry from financial, clinical and administrative applications. Single Sign-On is a powerful application and can be enabled very fast which means the user can save more time.
In the Single Sign-On system the user logs with his user ID and password in the given fields and gets access to relatively low risk information and also can access to enterprise portals. The Single Sign On Software requires stronger authentication when the user is accessing to high risk information applications such as payroll management system, which includes security tokens, digital certificates, biometrics and smart cards.
Single Sign On can also occur in between two enterprises using organized authentication. In this case we can consider the example as, an employee of the business partner can log into their organizations system, when he or she clicks on the link provided by the enterprise application, then the Single Sign-On Software vendor will provide a security to the enterprise with the help of some of the protocols like Liberty Alliance, WS Federation, SAML etc. Single Sign-On Software of the enterprises then receives the security token and checks it thoroughly and it gives access to the employee without any sign in.
Single Sign-On Software should check every single request by the user’s browser to see is there an authentication policy referring to the application to which the user is trying to access. Whenever a user clicks on a URL in medium or larger enterprises there is traffic between the user’s browser and the security server, there every chance that this traffic can increase from the point of performance. In this scenario most of the SSO Solutions use directories like Light Weight Directory Protocol (LDAP) to store the authorization and authentication policies. These directories are meant for high performance, which can manage heavy traffic load. LDAP are often considered as a better resource for a SSO system against authentication.
In the small and medium enterprises, the enterprises can become single point of failure, if the Single Sign On application is not designed properly. No user can access any application protected by the Single Sign-On Software if the system goes down and the application or resource remains up. This uncertainty in the SSO results in productivity loss to the enterprises. Hence every enterprise whether it is large or medium should make sure that they a well-tested failover and disaster recovery design Single Sign-On system.
Whether it is small or medium enterprises it requires high standard identity data governance. All enterprises should have good and quick business process which can match with any changes such as identify termination, role changes, new identity creation etc. if the these changes are not practiced by the enterprises then their SSO application can be easily accessible and open to threats.
CPL.THALESGROUP

Thales building an encryption strategy, licensing software, providing trusted access to the cloud, or meeting compliance mandates, you can rely on Thales to secure your digital transformation.
- Users – A single credential set for all cloud apps
- IT – Centralized cloud access management and fewer help desk tickets
- Security officers – A single audit trail of cloud access events
AVATIER
Avatier identity management software automates IT operations and corporate compliance of user provisioning, identity access management, corporate governance, enterprise risk management and password management.
- Instant Directory SSO Authentication
- SaaS License Management
- Integrated Identity Management
- Terms of Use Tracker
- Auto Launch Hide and Search SSO Apps
- Cloud Applications Control
- Enterprise Password Synchronization
- Enterprise Controlled SSO Portal
- Secure Cloud Admin Accounts
- Enterprise Controlled SSO Portal
- One Click Connection
- Session & App Usage Monitoring
OKTA
The Okta Identity Cloud provides secure identity management with Single Sign-On, Multi-factor Authentication, Lifecycle Management (Provisioning), and more.
- Always On Single Sign-on
- Customizable User Experience
- Secure Directory with Integration
- Real-time Security Reporting
- Adaptive Authentication
RIPPLING
Manage your business’s HR and IT- from payroll and benefits, to employee computers and software – all in one, easy-to-use platform.
- Give Your Team 1-Click Access to All Their Apps
- Access Any App, Anywhere, In 1-Click. Backed by 2FA
- See Who Accessed What, When & Where
- Connect New Apps In Seconds
SAP
Protect your users from identity theft and cyberattacks – while reducing IT security risks, costs, and effort – with SAP Single Sign-On (SAP SSO).
- Increase productivity by allowing users to log in once to gain access to all of their accounts
- Add vital security functionality to SAP and non-SAP software landscapes
- Ensure confidentiality through reliable, standards-based encryption during data transmission
- Protect against cybercrime using smart cards, two-factor and risk-based authentication, digital signatures, and encryption
- Reduce help desk costs by decreasing the number of calls made to recover passwords
MICROFOCUS
Micro Focus transforms your digital business with enterprise application software across DevOps, Hybrid IT Management, Security, Risk & Governance & Predictive Analytics.
- Access enterprise applications quickly and conveniently
- Provide a unified experience for accessing web-based applications
- Reduce or eliminate the cost of password resets
- Provide single sign-on (SSO) for SaaS applications
ONELOGIN
OneLogin’s IAM solutions securely connect people to technology with single sign-on and MFA.
- One Secure SSO Portal for All Apps
- Secure, Unified Endpoint Management
- Multiple Logins
- Social Login
- Personal Applications
- Language Support
- Shared Logins
PINGIDENTITY
Ping Identity frees the digital enterprise by providing secure access that enables the right people to access the right things, seamlessly and securely.
- Use adaptive authentication and SSO for one-click access to all your apps
- Optimize security and convenience with additional authentication factors
- Manage customer privacy and consent, and meet regulatory compliance
- Securely manage identity and profile data at scale
- Detect and block API cyberattacks using artificial intelligence
- Enable dynamic, real-time access security for apps and APIs
LEMONLDAP-NG
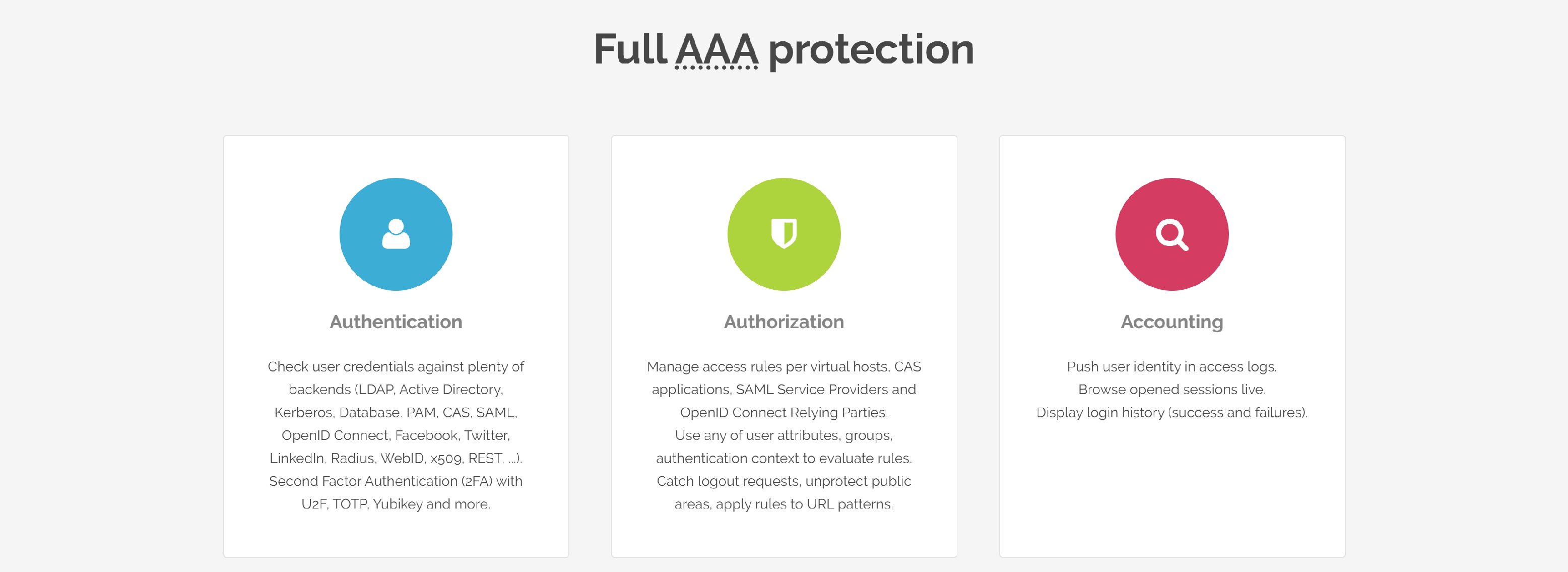
LemonLDAPNG is a free software to provide WebSSO, Access Management and Identity Federation.
- Full access control
- Easy to customize
- Easy to integrate
- Unifying authentications (Identity Federation)
- Session explorer
- Session restrictions
- Notifications
IMPRIVATA
Imprivata enables healthcare securely by establishing trust between people, technology, and information.
- Securely authenticate users and centrally manage strong authentication options such as ID tokens, Windows and national ID smart cards, active and passive proximity cards, fingerprint biometrics, USB tokens and others
- Streamline application access by automating many of the common and redundant tasks of password security, including enabling software applications for single sign on, enforcing password policy, and changing passwords on behalf of users at required intervals
- Simplify reporting with the ability to demonstrate regulatory compliance more easily with a variety of canned and customized reports that show who had access to what data when, and from where
AUTHANVIL

AuthAnvil protects your company data with the best security practices available, with the power of multi-factor authentication and the efficiency of single sign-on.
- Simple. Seamless. Secure.
- AuthAnvil SSO Launchpad
- AuthAnvil FastPass
- User Security Policy Management
FORTRA

At Fortra, we’re creating a simpler, stronger, and more straightforward future for cybersecurity by offering a portfolio of integrated and scalable security solutions.
- Implementation of SSO between Windows-based workstations and AIX, IBM i, Unix and Linux systems in as little as one day
- Hands-on implementation training with an experienced SSO expert
- Ongoing tech support to proactively address issues introduced by OS or application updates
Password Authentication
We all live in the world of technology where everything issecurely unsecured where the user identity is not secured. There is every chance that a stranger can get access your to user data and steal the confidential information in not time, if the Password Authentication is not properly authenticated. Even though it is the weakest form of Authentication most of the Enterprises still relay on the same old user Password Authentication. Enterprises put every effort to strengthen the password but they could match up to the modern hackers.
A hardware keyboard logger was the first tool used to attack against password authentication, which are legally available online to buy at $40 and these are devices connected to the keyboard and computer. The hardware keyboard logger records each and every keystroke with some model which enables to date stamps and time against the data. The hardware keyboard logger is similar to a small piece of hardware that is connected to the computer and which takes only 10 seconds to install and which cannot be detected by any means of software’s available in the market.
Hackers have come up with new ways to hack the user passwords which further weakened the usage of password authentication. The password authentication logging software programs are embedded in the email which are activated by clicking on the links provided in the emails or by accessing a fake website which in all means looks like a regular website.
A group of well-organized web hackers have developed the software called keyboard logging software which will recognize the authentication passwords and user bank id, that the user enters logon to the banks website for transaction. Once these details are entered by the user the next second user id and password are sent to the organized crime servers, then the received user details are auctioned online to other web criminals and in no time users bank account will be emptied.
Use Single Sign On Software services to avoid these kind of criminal activities and be safe and protected all the time. Some precautions have to be followed by the user to strengthen the password like layered identity defence strategy, which means your enterprise will allow the use of user id and password to gain only general access to very low risk enterprise application and information for example the enterprises website. But when the user is trying to access applications which are higher risk then the enterprise should require stronger password authentication. In the process you should include the usage of digital certificates, smart cards, biometrics and security tokens.