Executive phishing is an attack that targets high-level executives in a company, and it has been on the rise since 2013. It’s also not your average spam email. Executive phishing emails look very legitimate and often include malicious attachment files, links to a fake website, or requests for fraudulent wire transfers.

This blog post looks at executive phishing attacks. Why they are happening more frequently now than ever before, what the danger of these phishing attacks are to you personally as well as your company, and how you can avoid them completely.
What is executive phishing?
An executive phishing attack is an email that targets a high-level employee in a company, usually someone who has access to sensitive information. In order for the person receiving the “phish” to fall prey and click on malicious links or attachments, they need to have been trained well enough not to do so, which means it can sometimes be difficult to detect executive phishing emails.
Who is at target in executive phishing attacks?
People who receive these phishing emails are often those in the accounting, human resources, or legal departments. This is because they usually have access to sensitive data such as employee contact information and payroll records.
These types of employees also tend to be very busy, which means that if an email comes through requesting a wire transfer immediately before the end of the day, it might be easy to just click on the link and complete the transfer without thinking twice.
In addition to this, organisations should perform penetration tests and vulnerability scanning on regular basis to avoid getting prey to other cyberattacks also.
What are the dangers of an executive phishing attack?
As executive phishing attacks are very personalised, they can be incredibly effective at damaging reputations, especially if sensitive data is leaked or money gets stolen from a compromised executive’s account.
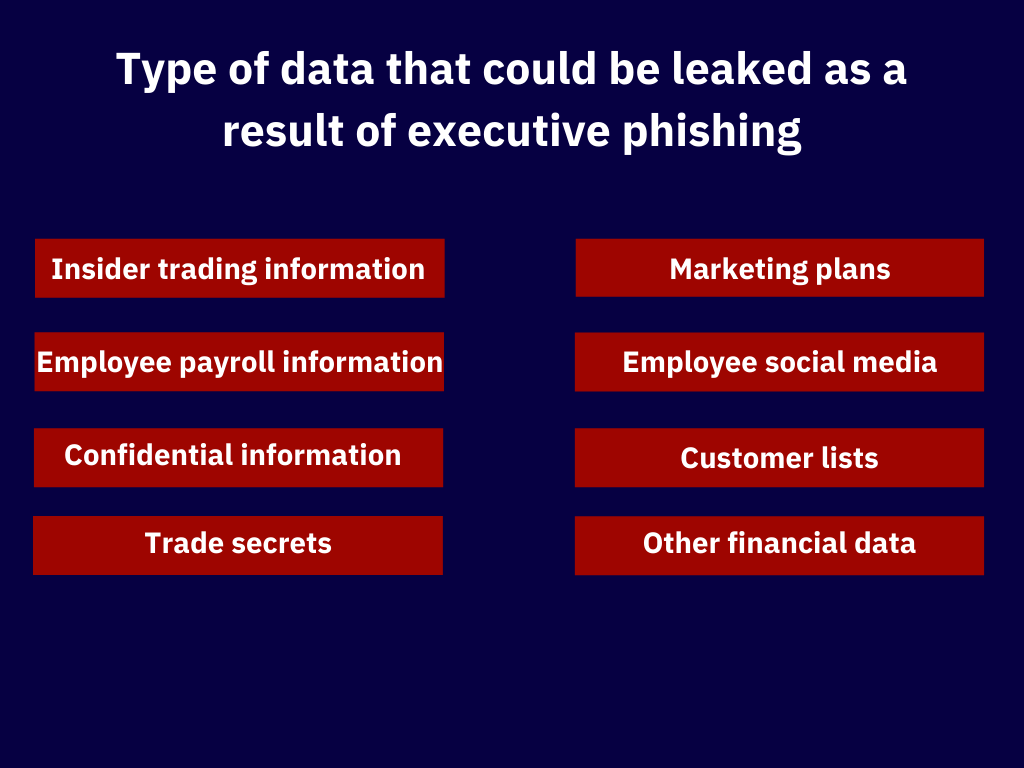
If you’re wondering what information attackers could get their hands on when targeting an executive, think about the following:
Insider trading information
If a competitor gets to know that your company is about to purchase another, they could buy stock in this other company and make a lot of money, leaving you with nothing.
Employee payroll information
This includes Social Security numbers and salary history, which can be used for identity theft or blackmailing purposes if mishandled by the perpetrator.
Confidential company information
Attackers can use this to create targeted spam campaigns or focus their attacks on specific departments in your business.
Trade secrets
If attackers manage to gain the ability to wire money, they could steal your company’s trade secrets and sell them for profit.
Sensitive business deals or marketing plans
If marketing plans and other sensitive business deals information leaked to a competitor, this will give them the upper hand.
Employee social media or the email account
Attackers can use this type of data to get access to employees accounts on social media sites for blackmailing purposes if mishandled by the perpetrator.
Customer lists
If cyber attackers become able to get their hands on your customer list, they could use it for targeted spam attacks or sell it off.
Other financial data
This includes past and present financial information, payment records, bank account information. All of which can be used for malicious purposes if mishandled by the perpetrator.
All of these things can put a company’s reputation or even its solvency at risk if an attacker gets their hands on it. If money is stolen from accounts as a result of this attack, it can put a company out of business or cause massive layoffs.
Different types of executive phishing

Executives in companies are under constant threat of phishing attacks. In the past few years, a huge rise in these kinds of scams that target high-level employees has been seen. Here are just some types of an executive phishing attempt to watch out for:
Spear phishing attacks
A Spear phishing attack happens when an attacker targets only one person with personalised messages and requests tailored to them. Spear phishing attacks are very specific and personalised, which often makes them difficult to detect, especially when you don’t know who might be out for revenge or trying to sabotage your company in the long run.
Phishing kits
These are pre-prepared kits that are sold on the dark web, which attackers can then use to generate personalised text messages for their phishing scams. This makes it possible for even those with little technical knowledge to launch an attack on a high-level executive in a company, making these types of attacks extremely dangerous and hard to detect.
Whaling attacks
Whaling attacks are like spear-phishing but specifically target high-level executives such as CEOs and CFOs. The ultimate goal of a whaling attack is to use high-level executives in order to gain access. For example, by sending an email that appears like it’s from the CEO and requesting a wire transfer right away.
Vishing
Voice phishing or vishing is a form of phishing in which the user is contacted over the phone. The person receiving the call might be asked to enter their username and password or even transfer funds through this method right away, which can be very dangerous when they are not aware that someone who does not have permission is trying to access their account without them knowing about it.
Money mule
This type of executive phishing scam targets people who might be looking for extra money or have been offered payment through courier services or other shady means. The attack involves someone offering payment to a company employee in exchange for money or data, and the attacker might even offer an “incentive” such as free concert tickets or merchandise if they follow through with this activity.
What is the solution to executive phishing?
As you can see, it’s incredibly dangerous for high-level employees to fall prey to these types of cyber-attacks because they tend to have access not only to sensitive company data but also money and other things that could put their companies at risk.
If you have been a target of an executive phishing scam, you should contact legal authorities or a cyber security firm to manage any future data loss and provide you with the best solution to get out of the situation.
Tips to protect yourself against executive phishing
Here are some tips for you to avoid falling prey to these types of scams:
1. Be aware that your information could be compromised and monitor your accounts for anything suspicious.
2. Know that requests like transferring money to different locations or providing sensitive data might be part of an executive phishing scam and do not comply with them unless you are absolutely certain that they come from someone who has permission to request such things (such as the CEO).
3. Be aware of any strange phone calls you might receive asking for personal information or money transfers.
4. Do not trust emails that request banking information, wire transfers, etc., without verifying them first. Even, if they seem to have come from a legitimate source, such as your CEO or CFO, it’s best to contact the sender and make sure they actually sent that email.
5. Be careful not to download attachments in emails without verifying them first because this could also lead to downloading malware infection and data breaches.
6. Don’t click on links or download attachments from unknown senders. Instead, open a new window and go directly to the website in question. If you’re uncertain about an email, whether it is safe or not, just call the company’s customer service line to make sure.
7. If you receive emails asking for personal information, don’t provide the requested information. Instead, contact your company’s customer service line to confirm that it was actually sent by someone who has permission to request this type of data from you or a co-worker.
8. Don’t trust header information either because it might have been forged.
9. If you receive emails asking for wire transfers, don’t comply unless you have confirmed this request with your company’s customer service line first in order to avoid being scammed or putting the company at risk of fraud and other attacks.
10. People who are looking for extra money should be careful when it comes to accepting offers from strangers because it could very well be a scam.