Firewall log analysis is a process that involves examining the records generated by a firewall system to identify security threats or anomalies within a network. Firewall logs are critical for network administrators to detect, investigate, and prevent malicious activity such as unauthorized access to sensitive data, hacking attempts, and malware infections.
Discover the top 7 best Firewall Log Analyzer and Management Software Tools
ManageEngine Firewall Analyzer
ManageEngine Firewall Analyzer offers comprehensive firewall management and real-time monitoring for enhanced threat detection and prevention.
- Real-time monitoring and log analysis
- Automated compliance and security reporting
- Firewall policy management and optimization
- Traffic analysis and bandwidth monitoring
- User-friendly dashboard and customized reports
- Centralized log storage for easy access and retrieval
SOLARWINDS
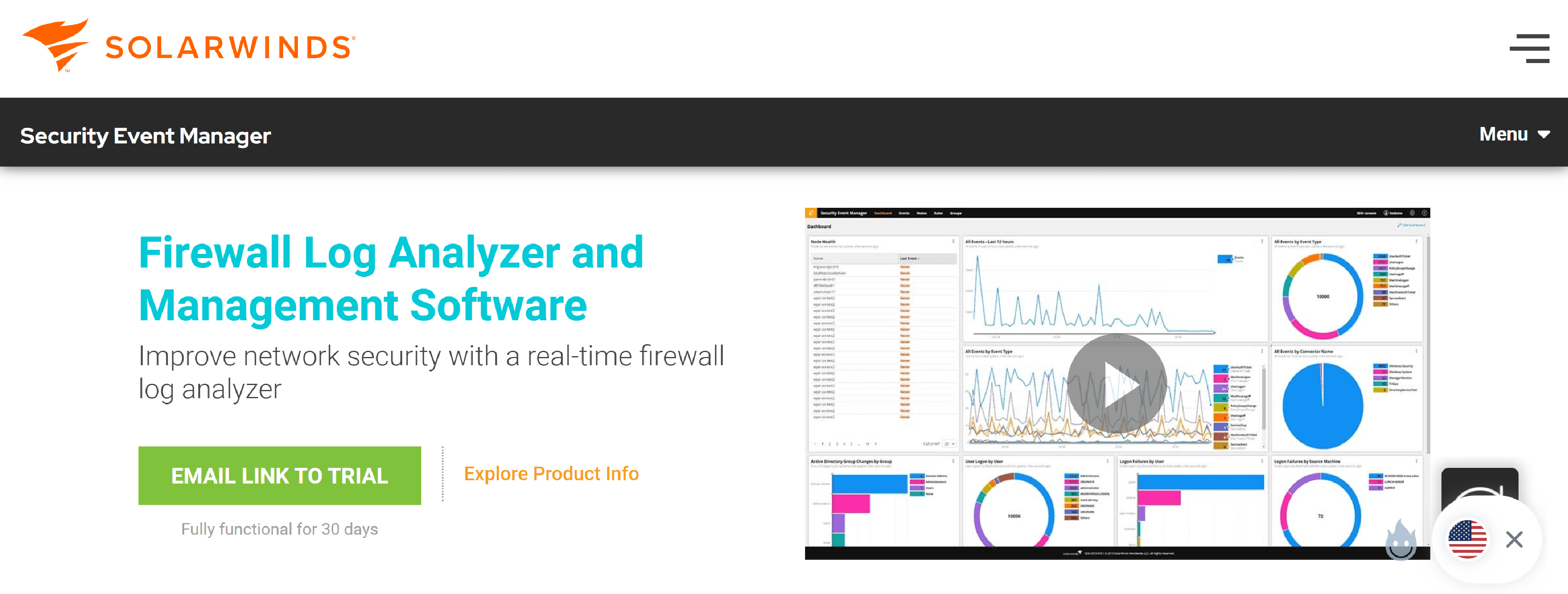
SolarWinds – firewall log analyzer tool automates threat remediation and helps secure networks against cyber attacks with customized event correlation rules.
- Centralize firewall logs on a single location
- Use custom or built-in correlation rules for better network visibility
- Secure your network against threats with automated active response
- Keep an eye on firewall activity by setting custom alerts
- Retain access to historic logs without exceeding storage capacity
LOGGLY
Loggly offers a cloud-based log management service that helps you aggregate and analyze all kinds of text-based logs for unified monitoring and troubleshooting.
- Aggregate all your network and firewall logs
- Extract better insights from your firewall logs
- Leverage multiple integrations for faster troubleshooting
PAPERTRAIL
Frustration-free log management. Seamlessly manage logs from apps, servers, and cloud services.
- Aggregate and scan all your logs
- Speed up root cause analysis
- Detect incidents and anomalies sooner
NETWRIX ( Netwrix Auditor, Netwrix Change Tracker )

Netwrix threat detection software from Netwrix and get the tool you need to catch complex attacks on the fly.
- Real-time alerting
- Integration with other security technologies
- Automated response
- Machine learning and user behavior analytics
- Deception tools
- Auto-adjusting to risk behaviors
WEBFWLOG
Webfwlog is a flexible web-based firewall log analyzer and reporting tool. It supports standard system logs for linux, FreeBSD, OpenBSD, NetBSD, Solaris, Irix, OS X, etc. as well as Windows XP®.
- Poor security track-record
- Favorable security track-record
- Many reported vulnerabilities
- Few reported vulnerabilities
MOTADATA
Motadata дog management tool that helps organizations to collect, analyze, monitor, and visualize the log data for rapid troubleshooting of issues.
- Monitors & optimizes the entire IT infrastructure
- Monitors the network ensuring maximum uptime
- Provides customizable dashboards and widgets
- Provides actionable operational intelligence insights
TUFIN
![]()
Tufin’s pre-defined compliance report templates make it easy for organizations to get an accurate, updated view of their security posture in the context of regulatory requirements within minutes.
- Centralize Firewall Audit Reporting
- Continuous Compliance Automation
- Fix Firewall Rule Misconfigurations Fast
- Side-by-Side Change Comparison
- Simplify Network Firewall Management
- Run Real-Time Policy Compliance Checks