A secure web gateway (SWG) is a solution that provides organizations with a secure and controlled way of accessing the internet. It acts as the intermediary between the users and the internet, filtering their web traffic to protect against threats and enforce security policies. It combines various security technologies and features to ensure that users can safely browse the web and access cloud-based applications.
One of the main functions of an SWG is to protect against web-based threats such as viruses, malware, and phishing attacks. It accomplishes this by scanning web traffic in real-time, blocking access to malicious websites, and preventing the download of infected files. SWGs use a combination of techniques, including URL filtering, reputation analysis, and behavioral analysis to identify and block malicious content.
URL filtering is a technique used to categorize websites based on their content and apply specific policies to them. SWGs maintain a database of categorized URLs that they use to determine whether a website is safe or not. Based on the predefined security policies, the SWG either allows or blocks access to specific categories of websites. For example, an organization may want to block access to adult content or social media websites during working hours to enhance productivity.
Reputation analysis is another technique employed by SWGs to assess the trustworthiness of websites. It involves analyzing the reputation and history of a website to determine if it has been associated with any malicious activities in the past. Websites with a poor reputation are likely to be blocked or subjected to additional scrutiny before allowing access. This technique helps in preventing access to compromised websites that can exploit vulnerabilities in the user’s system.
Behavioral analysis is a more advanced technique used by SWGs to identify malware and zero-day threats. It involves monitoring the behavior of web content in real-time and comparing it against known patterns of malicious activity. SWGs can detect and block suspicious behavior, even if the threat is unknown or hasn’t been identified before. This helps in preventing the spread of new and evolving threats.
Besides protecting against web-based threats, SWGs also enforce security policies and provide visibility into web usage. They allow organizations to define rules and policies regarding web access, which can be based on various factors such as user roles, time of day, and location. These policies can be used to control access to specific websites or types of content, ensuring that employees adhere to the organization’s acceptable use policy. SWGs also provide detailed logs and reports on web activities, allowing organizations to monitor and analyze user behavior, identify potential security risks, and ensure compliance with regulations.
With the increasing adoption of cloud-based applications and the shift towards remote work, SWGs have evolved to include features that secure access to cloud resources. They provide secure access to cloud-based applications by acting as a proxy between the users and the cloud service providers. This ensures that all traffic between the users and the cloud is inspected and protected. SWGs can also integrate with cloud access security brokers (CASBs) to provide additional security and control over cloud applications.
A secure web gateway is a vital component of an organization’s security infrastructure. It protects against web-based threats, enforces security policies, and provides visibility into web usage. By combining various security technologies and features, SWGs enable organizations to safely embrace the internet and cloud-based applications while ensuring the security and integrity of their network.
LOOKOUT
Safeguard users, networks, and enterprise data from online threats with Lookout Secure Internet Access.
- Deliver the most optimal and secure user experience with a single proxy, single agent architecture
- Improve web application control
- Provide enhanced visibility and control across all cloud hosted, SaaS, and Internet traffic
- Quickly detect and prevent data exfiltration
- Filter URLs and content more effectively
- Define and enforce Acceptable Use Policy (AUP)
- Seamless TLS/SSL interception
CHECKPOINT
Check Point Harmony Connect cloud SWG prevents threats, controls access and protects data, so users are equally protected and productive when remote or in the office.
- Prevent Exploits in Real Time with a Cloud IPS
- Inspect All Traffic. Control All Access.
- Integrated Cloud SWG and FWaaS
- Single Client for Secure Internet and Private Access
ZSCALER
Zscaler is the leader in cybersecurity and zero trust digital transformation. Transform your IT and security needs with the best CASB and SWG solutions.
- AI-powered phishing detection
- AI-powered C2 detection
- AI-powered browser isolation
- Dynamic, risk-based access policy
- Correlated threat insights
- Cyber risk assessment
- HTTP/2 inspection
FORCEPOINT
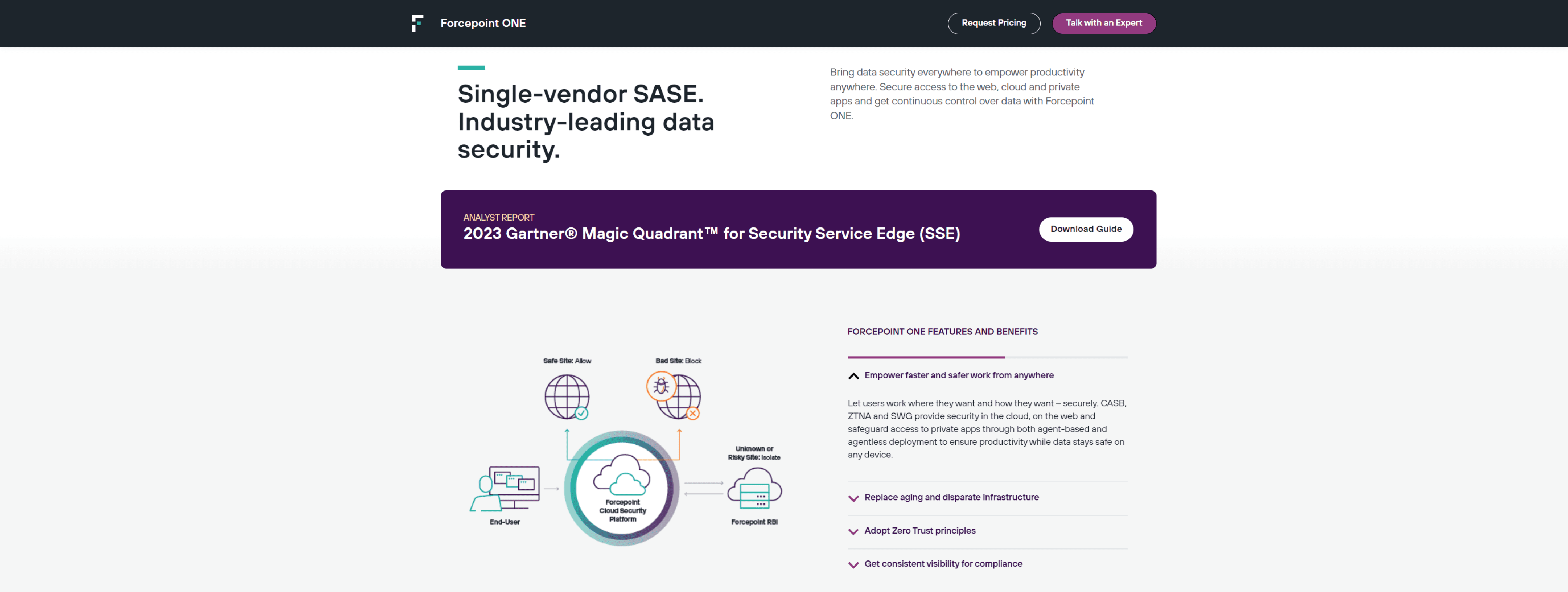
Forcepoint – protect data everywhere and secure access anywhere through Data-first SASE with the all-in-one, cloud-native security platform.
- Modernize Access for the Hybrid World
- Adopt Zero Trust Principles with Ease
- Secure Data Everywhere it Goes
- Track Economic Value and Security Posture in Real Time
NETSKOPE
Netskope Next Gen Secure Web Gateway (NG SWG) – web security delivered from the cloud to protect data, prevent threats, and control cloud apps.
- Visibility and control
- Advanced threat protection
- Advanced data protection
- TLS inspection at cloud scale
- Advanced analytics and reporting
PERIMETER81
Perimeter 81’s Hybrid SWG protects employees online. Block risky websites, set web filtering based on context, and protect from malware.
- Flexible Browsing Policies
- Enforce On-Network Rules
- Worry-Free Compliance
- Better Employee Privacy
A10NETWORKS
A10 Networks: next-gen Secure Web Gateway solutions. Advanced Load Balancing solutions to harden your network against today’s cyber attacks.
- Ever-evolving, modern cyber attacks
- Unfiltered internet access is risky
- Non-compliance is costly
SKYHIGHSECURITY
Skyhigh Secure Web Gateway (SWG) the complete solution protecting both users & data. Integrated RBI, CASB, industry leading DLP 99.999% uptime.
- Secure Uninterrupted Access
- Protection From Unknown Threats
- Advanced Data Protection
- Application Visibility and Control
- Skyhigh Cloud Firewall
NORDLAYER
NordLayer – secure network access solutions tailored to evolving business needs. Designed to save your IT admins time with seamless implementation into existing setups.
- Secure remote workforces
- Protect company resources
- Multiple connections
- Secure access to the internet
AXISSECURITY
Axis Security uses SSE to elevate access security and ensure that your connectivity is always in-sync with your business.
- Office or mobile employee attempts to access the Internet
- Atmos proxies and inspects traffic
- Atmos validates identity & applies policy
- Atmos fluently connects to Internet resource
- Atmos remains in line and monitors user experience
CATONETWORKS
Cato SASE Cloud converges SD-WAN, security, global backbone, and remote access into a global cloud-native service.
- Full visibility
- Unrestricted scalability
- Full traffic inspection with no degredation
- Self-maintaining cloud service